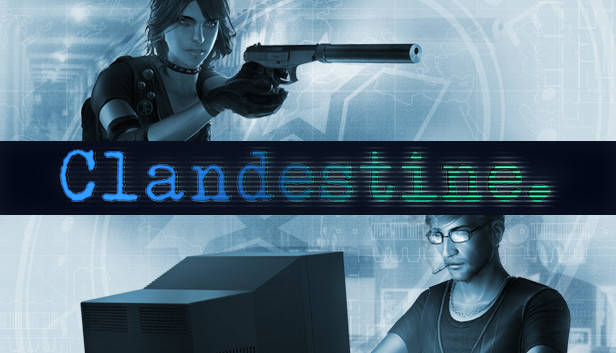
Clandestine
About this game
Clandestine is a 2-player or singleplayer stealth/hacking game set in 1996. Asymmetrical co-op allows one player to take the role of the spy while a friend provides overwatch and assistance as the hacker, and unravel a post-Cold War espionage conspiracy.
The year is 1996, five years after the dissolution of the Soviet Union. A string of accidents and murders gone mostly unnoticed by the public eye have put the world of international espionage on high alert - veteran Cold War operatives from both sides of the former Iron Curtain are being assassinated around the globe. High-ranking officials of the CIA and the FSB secretly establish a joint task force to investigate the leaks. Codenamed The Kingbridge Executive, the group is funded with whatever money could be skimmed off of official projects and staffed by whoever could be spared from official operations. As field operative Katya Kozlova or hacker Martin Symborski, you will be deployed on dangerous missions across Europe and North America, chasing the source of the leaks.
Key Features:
- Single Player & Asymmetrical co-op: Play as the spy while a friend guides you through the missions or take on the role of the hacker to crack infrastructure and defeat security systems.
- A return to hard-core stealth games where the enemies are lethal and combat is unforgiving.
- A deep hacking system built around core stealth game mechanics, rife with options to manipulate the game world and mess with your enemies.
- Use social engineering in cooperative dialogue sequences to bypass security checkpoints and gain entry to restricted areas.
- Your actions won't go unnoticed - the story will respond to how much evidence you leave in each mission and how many dead bodies you leave in your wake.
- Playing as the Spy. The role of the Spy will be familiar to fans of stealth/action games. As the Spy, you will experience Clandestine as a 3rd person game, controlling the movements and actions of Katya in the game world. Katya is the boots on the ground, armed with weapons and gadgets that you can use to stay alive and evade your opponents. Katya is also well trained in hand-to-hand combat, and can use lethal or non-lethal stealth takedowns to take down enemies, leaving behind as little evidence as possible. During the mission, it also falls to the Spy to search for dossiers and intel to unlock new equipment and software for subsequent missions.
- Playing as the Hacker. Martin operates in an entirely different way than the spy, which is reflected in the hacker player's interface and game mechanics. As the Hacker, players have access to four game windows and a toolbar. These game windows are: the Camera Feed, the Console, the Network View, and the Tactical Map.
- Camera Feed. The Camera Feed allows the hacker to observe the game world and scout ahead for the Spy. By default, the Camera Feed displays the Operative Camera (a hidden camera worn by Katya), but you can also jump into surveillance cameras on the Tactical Map (see below) to look through them and scout the levels for enemies and other threats. The Camera Feed also displays the status of the Spy's health.
- Console. The Console always displays game Objectives at the top of the window and prints important information in the Message Log such as cracked keypad codes. You can also use it to communicate with the Spy via the in-game text chat.
- Network View. The Network View window is where Hackers can access the computer network(s) which run all of the electronic infrastructure in the mission area. This includes door keypads, PCs, Servers, Firewalls, and Hazards (steam pipes and electrical boxes which can be triggered to cause "accidents"). Hackers must be mindful of the Network Admin, an enemy AI which searches for changes in the Network and tries to correct them. Not only will the Admin kick a hacker from the Network if caught, the Admin will also reset firewalls and pass-codes. Hackers can unlock Viruses and DDOS attacks to keep the Admin busy when trying to escape or complete an objective.
- Tactical Map. The Tactical Map is the window Hackers use to provide direct support to their Spy partners. This includes gaining access to cameras for scouting and observation, tagging enemies so the spy can track their location without maintaining line-of-sight, and use Local Assets to drop ammo or health, "clean up" bodies, cancel alarms before they sound, and even bribe enemies.






























Сomments